Non-security reason to prefer cookies for auth
April 08, 2026There are many discussions online about whether it is safe to store authentication tokens in the browser localStorage1. Apart from the security discsussion there is another compelling reason to favor cookies: Cookies are sent on every request to the server. This makes life easier when testing endpoints, for example while troubleshooting issues in production.
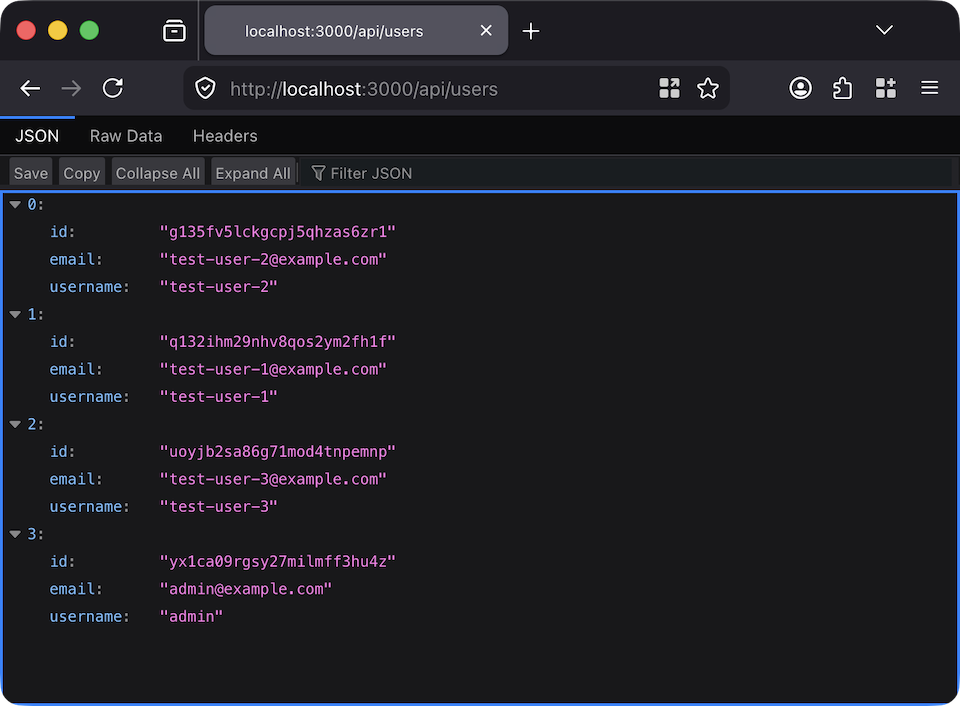
Opening a URL in the browser
Paste the URL of any protected API endpoint into the browser's address bar and access the results.
Running fetch in the browser console
You can run
fetch against a protected API endpoint and access the results.
Swagger docs
Authentication works seamlessly in Swagger with no additional configuration.
The three use cases above all become more cumbersome (or impossible) when auth tokens are stored in localStorage instead of cookies.
- One side generally argues against using localStorage because your tokens can be stolen in a XSS attack. The other side generally argues that this not the right thing to worry about - through XSS the attacker can steal all the user's data, including their username and password anyway. I don't find the counterargument convincing. HTTP-only cookies are meaningfully more secure than localStorage.